Introduction
Introduction
November 2023 marked a continued escalation in the Israel-Palestine cyber conflict. This blog builds upon our Cyber Conflict Analysis: Israel-Palestine 2023 (Master Thread) to dissect the key developments and strategic shifts in the cyber domain that occurred during this month.
For the previous analysis, for October 2023, see: 🌐 An Analysis of the Israel-Palestine Conflict from a Cybersecurity Perspective, October 2023
 Diversifying Cyber Warfare Tactics
Diversifying Cyber Warfare Tactics
In November 2023, the cyber warfare landscape witnessed a diversification in tactics used by various actors. Two notable incidents stood out for their sophistication and impact:
- MuddyWater Spear-Phishing Campaign:
- This campaign, linked to the Iranian nation-state actor MuddyWater, targeted Israeli entities using a sophisticated spear-phishing approach. The objective was to deploy a remote administration tool, “Advanced Monitoring Agent” from N-able.
- MuddyWater is part of Iran’s Ministry of Intelligence and Security (MOIS) and has been active since at least 2017. This group is known for its cyber espionage activities.
- The attack involved a multi-stage infection vector using a new file-sharing service called Storyblok. It began with hidden files, including an LNK file to initiate the infection, and an executable file designed to execute the Advanced Monitoring Agent while displaying a decoy document.
- The infection allowed MuddyWater operators to perform reconnaissance on the targeted systems. The lure document used was an official memo from the Israeli Civil Service Commission, indicating a well-planned operation leveraging a new C2 framework called MuddyC2Go.
- ChatGPT Targeted by Anonymous Sudan:
- OpenAI’s ChatGPT was reportedly targeted in a successful DDoS (Distributed Denial of Service) attack, attributed to the group Anonymous Sudan. This marked a significant incident, given ChatGPT’s extensive user base and its role in AI-based tasks.
- The attack caused repeated service outages for ChatGPT and its connected tools, impacting both developers and users. The nature of the outages suggested a DDoS attack, a common tactic used to overload and disrupt services by flooding them with requests.
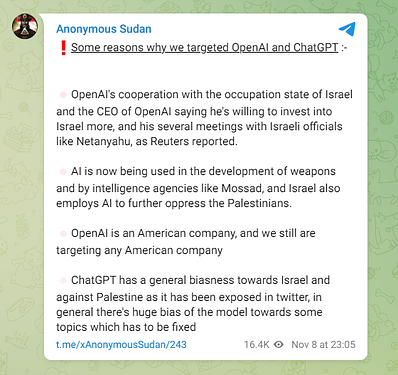
- Anonymous Sudan, a hacktivist group known for targeting systems for politically motivated goals, was identified as the perpetrator. This group’s recent targets have included systems such as Sweden’s NATO systems, their motives towards the ChatGPT attack were posted in their Telegram group here: Telegram: Contact @xAnonymousSudan. This included mentioning of ‘AI now being used in the development of weapons’. See the full post below:
These incidents highlight the evolving cyber battlefield, where strategies extend beyond traditional attacks into more nuanced domains like espionage and technological manipulation. The use of sophisticated spear-phishing tactics by state-sponsored groups and DDoS attacks targeting prominent AI platforms demonstrate a shift towards more diverse and complex forms of cyber warfare.
 Focal Points of Attack: Media, Technology, and Infrastructure
Focal Points of Attack: Media, Technology, and Infrastructure
November 2023 saw further tactics and focal points of cyber attacks within the Israel-Palestine conflict, affecting media, technology, and critical infrastructure:
- Anonymous Sudan’s DDoS Attack on AP News:
- The Associated Press (AP), reportedly fell victim to a DDoS (Distributed Denial of Service) attack by Anonymous Sudan. This resulted in sections of AP’s website going down for over 13 hours.
- Anonymous Sudan claimed responsibility for the attack on their Telegram channel. The group has become notorious for its high-profile DDoS attacks. For example, earlier in the year they were suspected to be involved in the Microsoft Outage
- Anonymous Sudan, suspected to be linked to Russia, has targeted various countries and organizations deemed as enemies of Islam. Their tactics align closely with those of Russian hacking gang Killnet, known for similar DDoS breaches.
- Deployment of BiBi-Windows Wiper Malware:
- Cybersecurity researchers warned about a new Windows version of wiper malware, dubbed BiBi-Windows Wiper by BlackBerry. This malware was a counterpart to the previously observed BiBi-Linux Wiper, used by a pro-Hamas hacktivist group.
- ESET, a Slovak cybersecurity firm, is tracking the actor behind the wiper under the name BiBiGun. The malware is designed to overwrite data in the C:\Users directory with junk data and append “.BiBi” to the filename. This effectively corrupts files and prevents recovery, as it also deletes shadow copies from the system.
- The larger campaign, suspected to be primarily targeting Israeli IT and government sectors, appears to be part of a strategy to disrupt day-to-day operations of Israeli companies using data destruction. The group behind the malware, called Karma, has been linked to another geopolitically motivated actor, Moses Staff, which is suspected to be of Iranian origin.
 Advanced Malware and Espionage Techniques
Advanced Malware and Espionage Techniques
In November 2023, the cyber warfare landscape saw an elevation in the complexity of malware and espionage techniques, particularly with the emergence of advanced malware variants like SysJoker and the strategic use of espionage tools such as the Pegasus spyware.
- SysJoker Malware:
- SysJoker, a multi-platform backdoor previously unattributed, was identified as being utilized by a Hamas-affiliated Advanced Persistent Threat (APT) to target Israel. This discovery by CheckPoint Research showcased a significant shift in malware sophistication, particularly with the transition to Rust language, indicating a complete rewrite of the malware while maintaining its functionalities.
- The new variants of SysJoker showed behavioral similarities with Operation Electric Powder, a series of targeted attacks against Israeli organizations between 2016-2017, which were linked to the Gaza Cybergang. This connection further highlights the strategic use of SysJoker in the ongoing cyber conflict.
- The Rust variant of SysJoker was particularly notable for its stealth and complexity. Submitted to VirusTotal under the guise of a typical executable (php-cgi.exe), it utilized random sleep intervals to evade detection and had two modes of operation based on its file path, demonstrating sophisticated evasion and persistence mechanisms.
- Pegasus Spyware:
- Israel’s military reportedly utilized Pegasus, the infamous spyware developed by NSO Group, to track hostages held by Hamas. This information, reported by Axios, revealed a strategic use of Pegasus in intelligence gathering and surveillance efforts, illustrating the role of such tools in modern conflict scenarios.
- The use of Pegasus in this context is significant as it demonstrates a shift from traditional espionage to more technologically advanced means. The collaboration with other tech firms to track and unlock phones of people missing since October 7th indicates the extent of integration of cyber tools in military and intelligence operations.
These developments in November 2023 represent a marked advancement in cyber warfare techniques, with entities deploying sophisticated malware and espionage tools not just for data breaches but for strategic intelligence and control. The use of SysJoker and Pegasus highlights a trend towards more complex, stealthy, and impactful cyber operations in the context of the Israel-Palestine conflict.
 Human and Global Implications
Human and Global Implications
The cyberattacks in November had significant human and global implications, especially with the Cyber Av3ngers’ attack on the U.S. Municipal Water Authority of Aliquippa, Pennsylvania.
- Cyber Av3ngers’ Attack on U.S. Water Utility:
- The Iranian-backed Cyber Av3ngers group compromised programmable logic controllers (PLCs) at the Municipal Water Authority of Aliquippa. This attack affected systems that monitor and regulate water pressure for thousands of customers, revealing the vulnerability of critical infrastructure to cyber threats.
- The quick response ensured no immediate risk to the public’s drinking water or water supply. However, it highlighted the broader vulnerability of public utilities to cyber threats and the need for improved cybersecurity measures.
- Wider Security and Regulatory Implications:
- The involvement of the FBI and CISA in the investigation into this incident reflects the serious national security concerns arising from cyberattacks on critical infrastructure. The incident underlines the necessity for enhanced cybersecurity practices and regulatory oversight, particularly in sectors like water management. This is also high priority to ensure hardened defence, that CISA are offering free vulnerability scanning for water utilities.
- International Cybersecurity Ramifications:
- The Cyber Av3ngers attack goes beyond national borders and reflects the global nature of cyber warfare. The global presence of Unitronics systems which has parts that are israeli-owned, used in the attacked infrastructure, points to the potential for similar attacks on critical infrastructure worldwide.
 Proactive Defense and Navigating Complex Cyber Threats
Proactive Defense and Navigating Complex Cyber Threats
As the cyber warfare landscape evolves, Israel’s proactive cyber defense strategies, particularly the strategic deployment of honeypots, exemplify the need for innovative measures to counteract the sophistication of cyberattacks.
- Strategic Deployment of Honeypots in Israel:
- Amidst its ongoing conflict with Hamas, Israel has significantly increased its deployment of honeypots. These decoy networks or systems are designed to lure hackers and enable cybersecurity experts to observe and understand hacker techniques and tactics.
- John Matherly, founder of Shodan, observed a notable rise in the number of honeypots in Israel, simulating a variety of products and services to capture any malicious activities across the country. This trend, starting in September, indicates heightened cybersecurity vigilance in Israel.
- Piotr Kijewski, CEO of the Shadowserver Foundation, confirmed the significant increase in deployed honeypots in Israel, propelling the country to the top three globally in terms of the number of deployed honeypots. This strategic move is a considerable elevation from Israel’s previous ranking and reflects its intensified focus on cybersecurity during the conflict.
- Silas Cutler, a resident hacker at the cybersecurity firm Stairwell, emphasized the tactical advantage of deploying honeypots during war. Such deployments can provide invaluable insights into adversaries’ attacker techniques and behaviour.
- NSA Insights on Israel’s Cyber Pressures:
- Rob Joyce, a senior official at the National Security Agency, pointed out that Israel is facing significant cyber pressure from various adversaries, including the Iranian government, hacktivists, and ransomware criminals. This underscores the complexity of the cyber threat landscape Israel is navigating amidst its conflict with Hamas.
- Joyce emphasized the challenges in distinguishing between independent hacktivist groups and those backed by nation-states. The use of misinformation, such as the false alerts on an Israeli missile strike warning app, has been a particularly impactful strategy used by adversaries.
 Conclusion
Conclusion
November 2023 in the Israel-Palestine cyber conflict has underscored the rapidly evolving landscape of cyber warfare. The diversification of cyber warfare tactics, ranging from sophisticated spear-phishing campaigns to strategic use of espionage tools, highlights the sophisticated methods of digital confrontation. The deployment of honeypots by Israel and the insights from the NSA on cyber pressures faced by the country illustrate the complexity of escalated cyber attacks. This month’s events reinforce the for robust cyber defense mechanisms and a comprehensive understanding of the cyber threat landscape. As cyber conflicts continue, the need for threat intelligence and international collaboration is more crucial than ever in securing companies, societies, and even physical infrastructure.
 Support the Cause
Support the Cause
In the wake of the ongoing conflict, numerous humanitarian organizations are working tirelessly to provide aid to those in need. If you wish to contribute, below are some platforms where you can make a donation (live as of November 2023):
 Support Palestinians in Gaza:
Support Palestinians in Gaza:
- Aid Children Affected by Gaza-Israel Conflict:
 Support Israel via Emergency Relief for Israel:
Support Israel via Emergency Relief for Israel:
Disclaimer: The inclusion of donation links does not imply endorsement of any particular stance on the conflict by Crushing Security. Participation is entirely voluntary, and individuals are encouraged to conduct their own research to ensure the authenticity and credibility of the platforms. Please adhere to the legal and ethical guidelines applicable in your jurisdiction when making a donation.
 Your Voice Matters
Your Voice Matters
We invite your perspectives and dialogue on this pivotal topic. Engage with us through the comments or reach out directly.
Connect with me on Twitter: https://twitter.com/cybersec_steve1